Microsoft’s Windows Recall tool is once again in question at a security level, after demonstrating that it is still possible to extract sensitive data using the TotalRecall Reloaded tool, even after its redesign with the incorporation of protection functions.
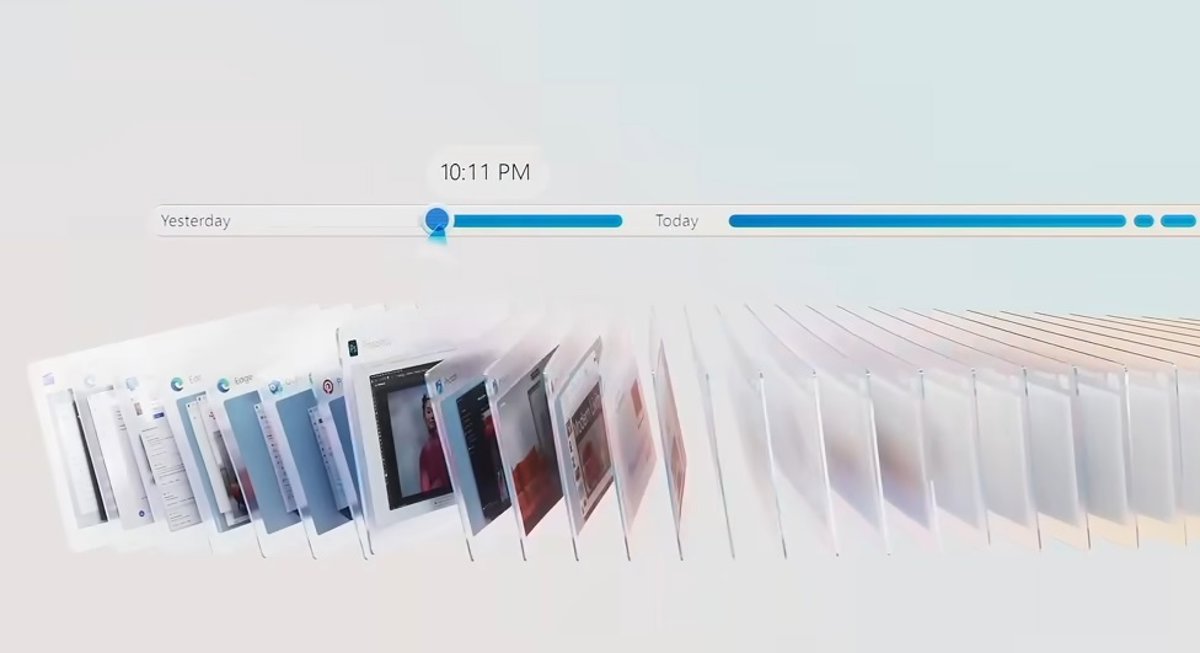
The Recall tool (memories) was announced in May 2024 as one of the artificial intelligence (AI) functions for Copilot+ computers, with the aim of helping the user return to previously searched content, both in ‘apps’, as well as in documents or websites. To do this, it periodically takes screenshots of the computer and creates a kind of ‘photographic memory’, which is collected on a timeline.
However, it had a controversial start because it was understood that it could put users’ private information at risk and that at first the captures were not stored encrypted. This led to postponing its launch on several occasions and incorporating new privacy and security measures, such as the obligation to use Windows Hello and the possibility of deactivating Memories of the operating system.
Finally, Microsoft released the final preview of Windows Recall in April of last year, as part of Windows 11 build 26100.3902, and detailed that it would arrive in the European Economic Area at the end of 2025.
Now, cybersecurity expert Alexander Hagenah has once again demonstrated that Recall continues to present serious security problems for usersdespite the modifications introduced by Microsoft.
Specifically, Microsoft’s redesign to add security to the tool was based on creating a secure vault for Recall data, hand in hand with authentication with Windows Hello and the virtualization-based Security Enclave, which is a secure environment for data.
According to Microsoft, these modifications restrict “latent malware attempts that attempt to accompany user authentication to steal data,” but the new tool developed by Hagenah, TotalRecall Reloaded, proves otherwise.
As he explained in a post shared through LinkedIn, his new tool can extract and visualize all the information that Recall’s photographic memory captures and stores.
Specifically, TotalRecall Reloaded runs silently in the background and is capable of activating the Recall timeline to “force the user to authenticate with a Windows Hello prompt.” Once Microsoft Recall is accessed using biometric credentials with Windows Hello, the tool takes the opportunity to enter the Recall tool and extract the data.
“My research shows that the vault is real, but the trust limit ends too soon,” Hagenah detailed, while recalling that Microsoft publicly stated that the redesign was intended to “restrict latent malware from being incorporated into user authentication, and that processes outside the enclave would only receive the data returned after authorization.” However, TotalRecall Reloaded “makes that latent malware stay with him.”
Following this line, he has stated that the scope is high and that TotalRecall Reloaded not only obtains screenshots, but also the history of text that has appeared on the user’s screen, email messages, documents, browsing context, timestamps and metadata generated by AI. “Together, they build a detailed behavioral profile of everything you do on your computer,” he warned.
MICROSOFT DISMISSALS VULNERABILITY
The expert reported his findings with TotalRecall Reloaded to Microsoft in early March, however, he noted that the technology company “closed the case” claiming that it is not a vulnerability.
“After careful investigation, we determined that the access patterns demonstrated are consistent with the intended protections and existing controls, and do not represent a circumvention of a security limit or unauthorized access to data,” said corporate vice president of Microsoft Security, David Weston, in statements to The Verge, while clarifying that the authorization period “has protection against time limit and hammering that limits the impact of malicious queries.”
However, also in statements to the aforementioned media, Hagenah has reiterated that the biggest drawback is that Microsoft claims that “the enclave prevents latent malware from circulating”, when “this is clearly not the case.”
This is because, based on its testing with TotalRecall Reloaded, it can pull the last cached screenshot from Windows Recall without requiring Windows Hello authentication or clearing capture history. Likewise, Hagenah also states that ‘malware’ can stay in the background on the PC and take screenshots by itself, without the need for Windows Recall.
It should be remembered that Microsoft is aware that the current implementation of Recall has not been successful and, therefore, it is rethinking its strategy, looking for a way to make it evolve, even if that means finding another name for it, as was recently announced.
Likewise, researcher Hagenah already revealed the initial security problems of Windows Recall with a first TotalRecall tool.
https://greatgolfbalsicas.es
https://www.reisezeit-online.de/afrika/glueckshotel-tunesien/
https://www.reisezeit-online.de/europa/fitness-urlaub-cervia/
https://www.reisezeit-online.de/europa/wassertemperatur-side/
https://www.reisezeit-online.de/australien/spinnensaison-australien/
https://bengal.blog/registration/
https://bengal.blog/
https://luckystarindia.it.com/en-in/
https://luckystarindia.it.com/en-in/app/
https://luckystarindia.it.com/en-in/android/
https://luckystarindia.it.com/en-in/ios/
https://luckystarindia.it.com/en-in/mobile/
https://luckystarindia.it.com/en-in/pc-client/
https://luckystarindia.it.com/en-in/registration/
https://luckystarindia.it.com/en-in/sign-up/
https://luckystarindia.it.com/en-in/login/
https://luckystarindia.it.com/en-in/verification/
https://luckystarindia.it.com/en-in/payments/
https://luckystarindia.it.com/en-in/deposit/
https://luckystarindia.it.com/en-in/withdrawal/
https://luckystarindia.it.com/en-in/bonuses/
https://luckystarindia.it.com/en-in/welcome-bonus/
https://luckystarindia.it.com/en-in/promo-code/
https://luckystarindia.it.com/en-in/live-casino/
https://luckystarindia.it.com/en-in/casino/